CompSec Direct is US based cyber operations focused company that provides cyber security software development and expert staffing. We provide Cyber to C4ISR vendors while developing small, tactical capabilities for: C2, deployable computers, cyber battle space visualizations, cyber ranges, information analysis and open-source reconnaissance. CompSec Direct offers professional services related to cyber security, and specialized cyber training.
We develop and staff ION’s, CNO Developers, Capability Developers and Subject Matter Experts within Cyber.
Our Locations
- US – Maryland 706 Crawfords Knoll Ct, Odenton, MD, 21113
- Puerto Rico – 151 Calle San Francisco, Suite 200, San Juan, PR, 00901
Our Credentials
- Maryland Consulting and Technical Services+ (CATS+)
- ISO 9001:2015 Certified Quality Management System
- ASG of Puerto Rico registered provider RUP #45269
- SDVOSB, SDB, MBE, Hispanic American Owned
- Trusted partner for public and private sector cybersecurity needs
- Proprietary Products and Services; we don’t resell things we don’t use or that we didn’t make ourselves.
Our Mission
At CompSec Direct, we are committed to delivering innovative cybersecurity solutions that protect critical assets, enhance operational efficiency, and ensure resilience against emerging threats.
Partner With Us
We are actively seeking new business partnerships to explore opportunities and drive innovation. Whether you’re looking for expert guidance, a trusted subcontractor, or a long-term collaboration, CompSec Direct is your go-to cybersecurity partner.
Get in Touch
Want to learn more about CompSec Direct and our services? Complete the form below, and a member of our team will get back to you promptly.
New Training: Advanced Agentic Workflows for Cybersecurity Research & Threat Intelligence
New CompSec Direct Training @Kleared4 Advanced Agentic Workflows for Cybersecurity [...]
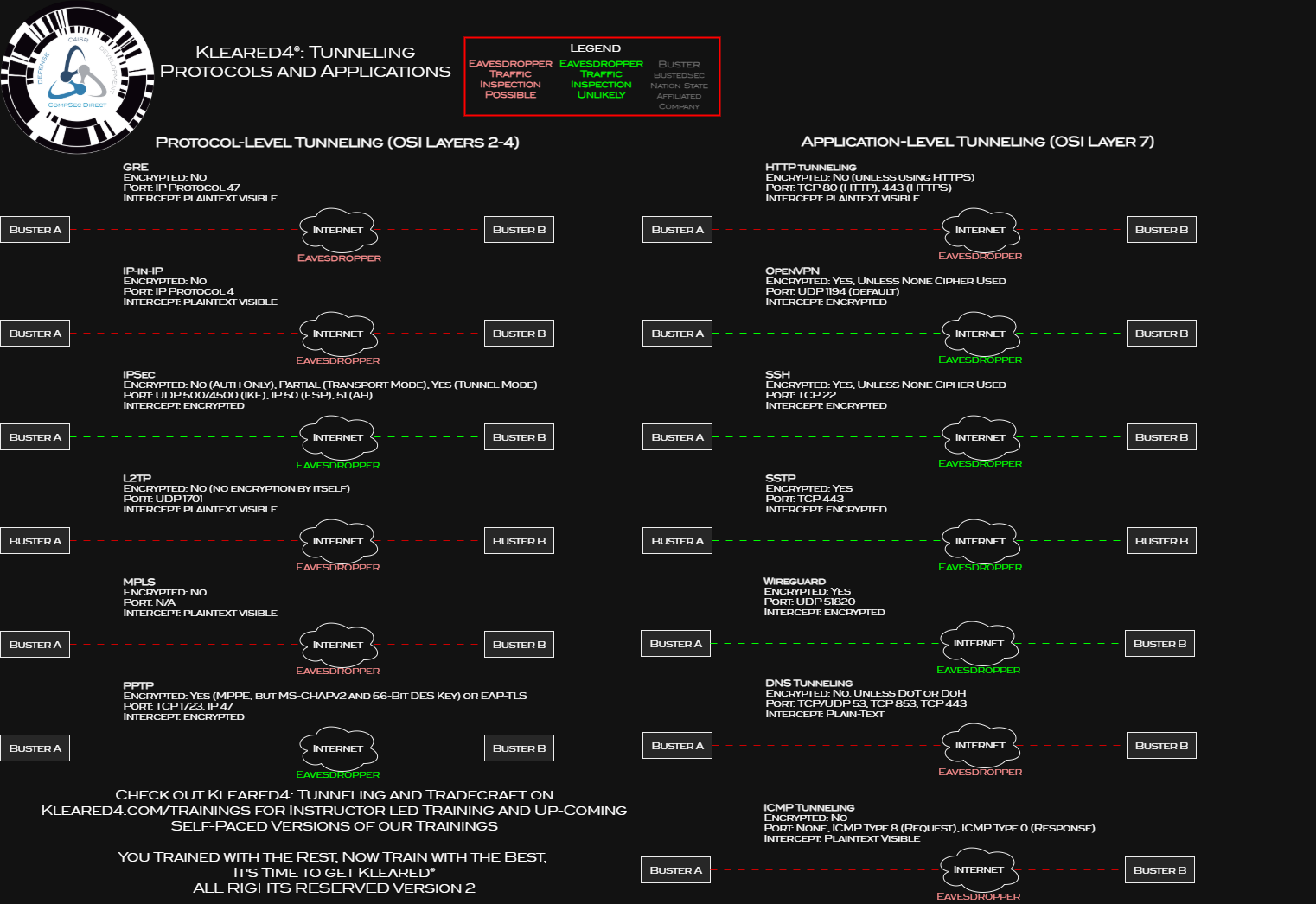
Cyber Range Training on Kleared4
Our class dates for cyber training have been updated for [...]
Intelligence Community (IC) BEC and Phishing leads to a bad day: Why using Kleared4 kicks ass
On July 17 2025, we received an email from an [...]
Breach Village Capture the Flag and Hack the Case
CompSec Direct ran Breach Village during a local BSides conference. [...]
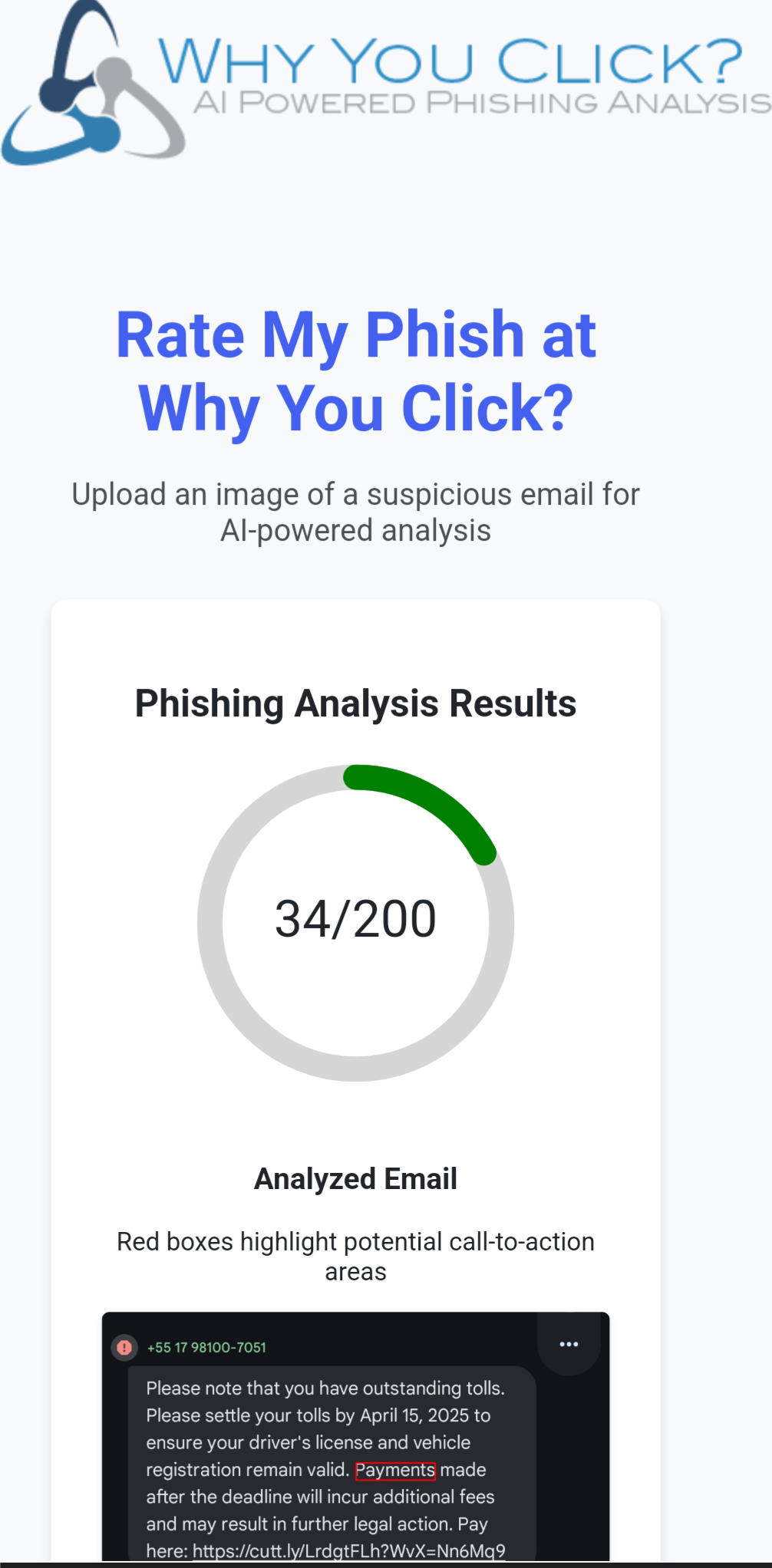
AI Powered Phishing Rating
CompSec Direct developed an AI powered phishing rater to determine [...]
Kleared4 Edge Fly Away Kits
During pandemic, we could not travel to customer locations and [...]
Why Choose CompSec Direct?
- Expertise: Decades of combined experience across federal and commercial sectors.
- Certifications: Fully certified to meet your organization’s security and contracting needs.
- Flexibility: Tailored solutions for businesses of all sizes, across industries.