Breach Village Capture the Flag and Hack the Case
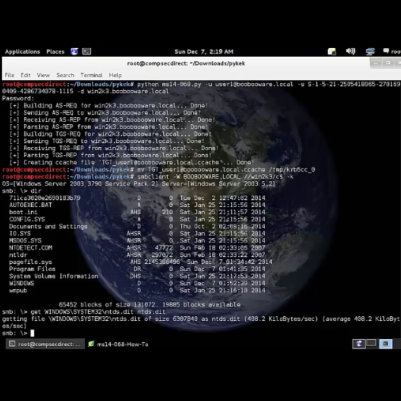
CompSec Direct2025-04-29T20:56:29-04:00CompSec Direct ran Breach Village during a local BSides conference. "We wanted Breach Village to showcase real-problems and not the made up scenarios people see in Capture the Flags events. Realism and modern problems in cyber security are difficult to showcase into a fun learning environment" said Jose Fernandez. Breach Village used our Kleared4 cyber range [...]