Bsides PR 2015 – Fun with Tor : How anonymity services complicate actor attribution CompSec Direct
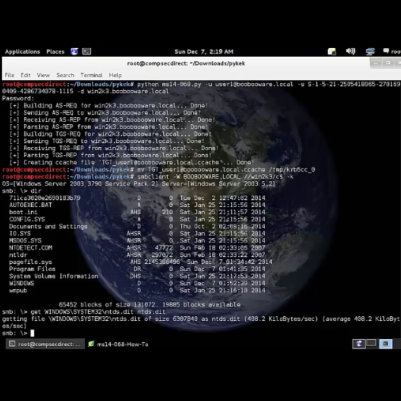
CompSec Direct2022-06-13T18:35:49-04:00Hello from Puerto Rico. Here are our slides from Jose Fernandez’s talk on Tor and attribution. We are very exited to have participated in BSides PR 2015, and look forward to speaking again in the future. By the time we got to the beach, the Internet is hopefully in a slightly better state than we left [...]